Hello everyone.
I have root access to the Hikvision camera through exploit and would like to recover admin password.
Most likely it's encrypted in the /etc/passwd file. Does anybody know what type of hash (or combination of hashes) is used there?
I'm asking about hash, because in my case I have double-digit salt Instead of 8 digits for md5:
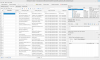
admin:$1$yi$xYzfgrVW7rmlj.tO2e5F.9:0:0:root:/:/bin/psh
Can you put here own TEST list from Hik Cam /etc/passwd for reverse engineering? I mean pass and hash at the same time.
Or is there another way to find the password in plain text from configuration files?
Dev_info:
{
"dev_status": 1,
"dev_subserial": "E001943964",
"dev_verification_code": "COLLOD",
"dev_serial": "DS-2CDVT-SFCMPTCN-S0120191218AAWRE43287690",
"dev_firmwareversion": "V5.5.95 build 190560",
"dev_type": "DS-2CDVT-SFCMPTCN-S",
"dev_typedisplay": "DS-2CD2456G5-I",
"dev_mac": "98:df:82:56:b6:6f",
"dev_nickname": "",
"dev_firmwareidentificationcode": "",
"dev_oeminfo": 0
}
I have root access to the Hikvision camera through exploit and would like to recover admin password.
Most likely it's encrypted in the /etc/passwd file. Does anybody know what type of hash (or combination of hashes) is used there?
I'm asking about hash, because in my case I have double-digit salt Instead of 8 digits for md5:
admin:$1$yi$xYzfgrVW7rmlj.tO2e5F.9:0:0:root:/:/bin/psh
Can you put here own TEST list from Hik Cam /etc/passwd for reverse engineering? I mean pass and hash at the same time.
Or is there another way to find the password in plain text from configuration files?
Dev_info:
{
"dev_status": 1,
"dev_subserial": "E001943964",
"dev_verification_code": "COLLOD",
"dev_serial": "DS-2CDVT-SFCMPTCN-S0120191218AAWRE43287690",
"dev_firmwareversion": "V5.5.95 build 190560",
"dev_type": "DS-2CDVT-SFCMPTCN-S",
"dev_typedisplay": "DS-2CD2456G5-I",
"dev_mac": "98:df:82:56:b6:6f",
"dev_nickname": "",
"dev_firmwareidentificationcode": "",
"dev_oeminfo": 0
}
Last edited: